Chances are, you are a lot closer to an online security disaster than you think. Information about you is spread out far and wide online, and losing control of this digital identity can be incredibly embarrassing at best and financially devastating or personally dangerous at worst.
While it may initially seem overwhelming, we’re here to help you stay protected online. We’ve created a list of all the steps to stay safe online. Since there is a lot of information, we suggest you work through it at your own pace.
GET SECURITY ALERTS, EXPERT TIPS – SIGN UP FOR KURT’S NEWSLETTER – THE CYBERGUY REPORT HERE

A woman stressed about an online disaster (Kurt “CyberGuy” Knutsson)
Step 1 – Enable automatic updates
Keeping your software up to date is one of the easiest ways to keep yourself safe online. Whether you are using a Windows machine, a Mac, an iPhone or an Android smartphone, all these devices are routinely updated with new security fixes. It’s a good idea to double-check and ensure your device’s automatic updates are turned on. Here’s how:
Windows 10 automatic updates
From the start menu, go to Settings > Update & Security > Windows Update. From the Windows Update section, you’ll see a range of options for updating Windows. Here you can set up your “active hours” to make sure that Windows reboots and installs automatic updates outside of your waking or working hours.
Windows 11 automatic updates
Windows 11 users will click the Windows icon and proceed to Settings > Windows Update > Advanced options. From here, you can control when Windows Update will run, similar to the “active hours” control in Windows 10.
macOS
Mac users can open System Preferences > Software Update and click the “Advanced” button. While in the “Advanced” section, make sure every box is checked, as this will ensure they receive timely OS updates.
iOS
If you want to turn on automatic updates with an iPhone, open Settings > General > Software Update and make sure that Automatic Updates is turned on.
Android
If you have an Android device, open Settings > System > Advanced > System Update and ensure the System Update setting is turned on.
AUTO PARTS GIANT EXPOSED: 2.3 CUSTOMERS AT RISK IN MASSIVE DATA BREACH
Step 2 – Use strong passwords
Reusing the same password on multiple websites or applications is one of the most common cybersecurity mistakes. If you use the same password for multiple things, it only takes one service breach to expose your other accounts. Using a password manager is an easy solution to creating strong passwords for multiple accounts.

Illustration of securing your device (Kurt “CyberGuy” Knutsson)
WORLD’S LARGEST STOLEN PASSWORD DATABASE UPLOADED TO CRIMINAL FORUM
Step 3 – Set up and use two-factor authentication
Two-factor authentication is a great way to add an extra layer of security to your online accounts. Enabling two-factor authentication makes it harder for hackers to access your account, as your account will require a one-time code in addition to the password to log in.
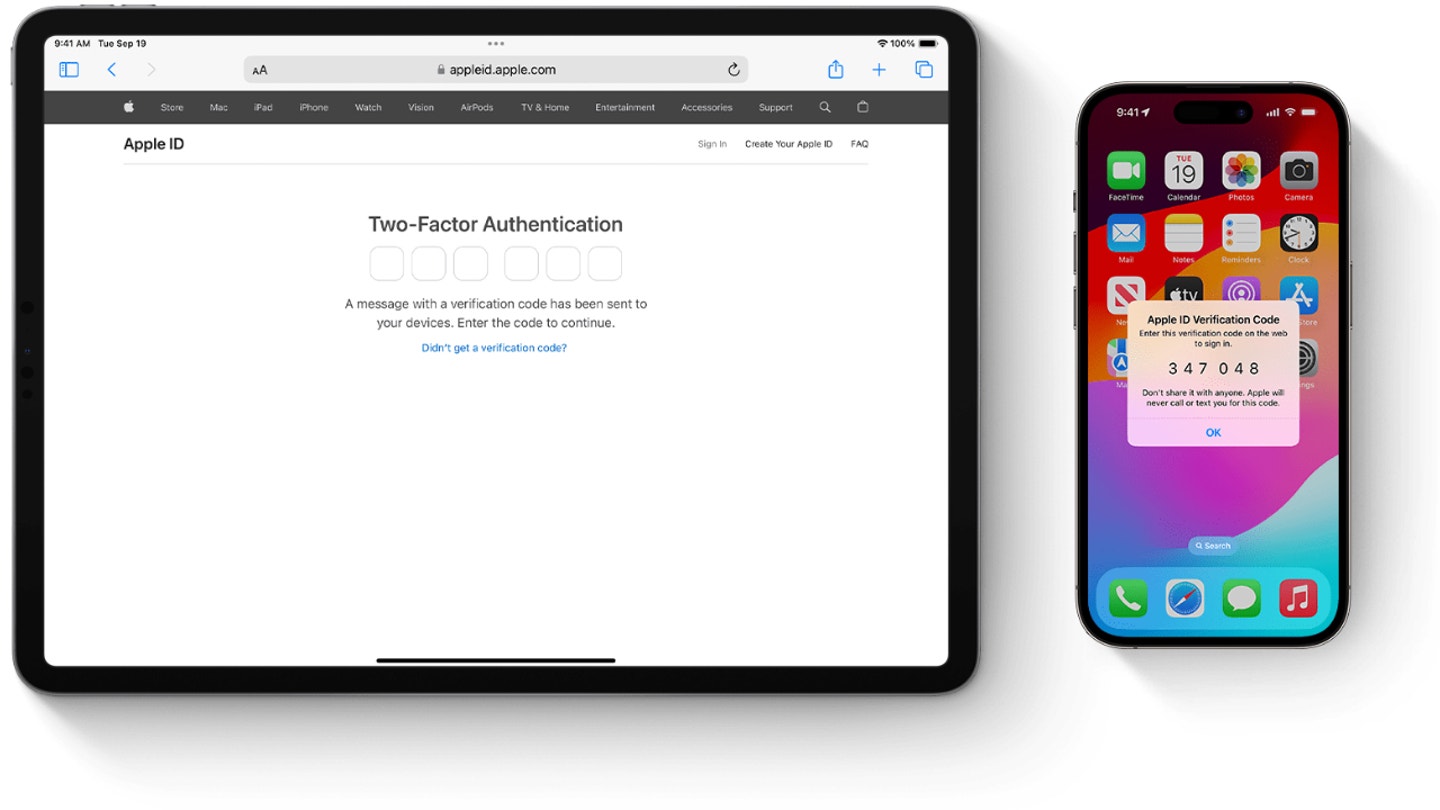
Two-factor authentication being displayed on Apple devices (Apple) (Kurt “CyberGuy” Knutsson)
Step 4 – Encrypt your computer’s storage
If you were to lose your laptop, tablet or phone, all of the personal information on those devices may be accessible to whoever finds it. An easy way to keep yourself safe in this scenario is to have your devices encrypted beforehand. Encryption makes the data hard for hackers to read, and while it sounds complicated, the actual process is easy to set up.

Illustration of data on a computer screen (Kurt “CyberGuy” Knutsson)
Step 5 – Locate or erase a lost device
If you’ve lost your device before you could encrypt it, there’s no need to worry too much. It’s easier than ever to locate a lost smartphone or to wipe it remotely. We have a great guide on what to do if you’ve lost your phone for both Androids and iPhones.
You can also use a similar process to locate a lost Windows laptop or MacBook. As operating systems have moved to storing information in the cloud, it’s easy to wipe a lost laptop. If you lose a laptop in public, we recommend remotely wiping it as soon as possible to ensure your data isn’t taken by a malicious actor.
Step 6 – Have strong antivirus software
The best way to protect yourself from clicking malicious links that install malware that may get access to your private information is to have antivirus protection installed on all your devices. This can also alert you of any phishing emails or ransomware scams. Get my picks for the best 2024 antivirus protection winners for your Windows, Mac, Android and iOS devices.
Step 7 – Secure your web browser
We use our web browsers daily. Whether from a laptop, a desktop or a smartphone, you probably use your web browser more than most other apps. Taking a few minutes to regularly update your browser to the latest version, being cautious about the websites you visit and avoiding suspicious downloads are all crucial practices that complement your browser’s security features.
By implementing these security measures, you’re protecting your browser, personal information, financial data and overall digital identity from being exposed to a security risk by potential hackers and cybercriminals.
Step 8 – Secure your smartphone
Smartphones now act as extensions of our personal lives, used for everything from banking to scheduling doctor appointments. It’s more important than ever to keep your smartphone secure, and fortunately, both Android and iOS feature a wide range of built-in features to help protect your personal information.
To enhance your iPhone or Android’s security, start by enabling a strong lock screen method such as a complex passcode, fingerprint recognition or facial recognition. Exercise caution when using public Wi-Fi networks and consider using a VPN for added security.

A person holding an Android phone (Kurt “CyberGuy” Knutsson)
10 SIMPLE STEPS TO IMPROVE YOUR SMARTPHONE’S SECURITY AND PRIVACY
Step 9 – Protect your wireless network
Your home Wi-Fi network can power your smart home devices, but it can also leave you vulnerable to hackers. Luckily, it’s easy to tweak your home wireless settings to keep yourself more protected. Similar to our previous steps, you’ll want to make sure your router has the most recent updated firmware and that you use two-factor authentication and a strong password for your wireless connection.

People on their computers using a wireless network (Kurt “CyberGuy” Knutsson)
Step 10 – Regularly back up your data
Regularly backing up your data protects your digital life from hardware failures, theft or cyberattacks. Choose a reliable backup method that suits your needs, such as cloud storage or external hard drives. Set up automatic backups to run consistently, ensuring all your devices, including smartphones and tablets, are covered. Secure your backups by using strong passwords, enabling two-factor authentication for cloud storage or encrypting physical backups.
Periodically, test your backups by restoring files to ensure the system works correctly. Remember, a solid backup strategy is an essential component of your overall cybersecurity plan, providing both protection and peace of mind.
Step 11 – Invest in personal data removal services
In today’s digital landscape, your personal information can end up in numerous online databases and people search sites without your knowledge or consent. These data aggregators collect and sell your information, potentially exposing you to privacy risks and unwanted solicitations. Using a data removal service can help mitigate these risks by systematically removing your personal information from these databases.
While no service promises to remove all your data from the internet, having a removal service is great if you want to constantly monitor and automate the process of removing your information from hundreds of sites continuously over a longer period of time.
By reducing your digital footprint, you decrease the chances of your personal information being misused for identity theft, targeted advertising or other privacy-invading practices. While it’s challenging to completely erase your online presence, using a data removal service is an effective step towards regaining control over your personal information and enhancing your overall online privacy and security. Check out my top picks for data removal services here.
Kurt’s key takeaways
Protecting your online presence might seem daunting, but remember, it’s all about taking small, consistent steps. Think of it as building a digital fortress: each measure you implement is another brick in your wall of cybersecurity. Don’t feel pressured to tackle everything at once. Start with the basics, like enabling automatic updates and using strong passwords, then gradually work your way through the more steps. The digital world is constantly evolving and so should our security practices.
How has your approach to online security changed over the years and what prompted those changes? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.

